v1.3.0 — DNS providers management (Cloudflare + Route 53)¶
Minor release. Consolidates the work from v1.3.0-alpha (backend + Option 2 pipeline) and v1.3.0-beta (UI) into a stable general release. No API changes, no new features versus beta.
Highlights¶
- Native Route 53 support for ACME DNS-01 alongside the existing Cloudflare integration. The custom Caddy image now bundles
caddy-dns/cloudflareandcaddy-dns/route53, and the host form picks between the two with a dropdown. - Panel-managed credentials, encrypted at rest. A new
dns_providerstable stores per-provider credential blobs AES-GCM-encrypted underARGOS_MASTER_KEY— the same master key that already protects OIDC client secrets, manual-cert private keys, and the VAPID signing key. Operators no longer need DNS tokens in.env. - Option 2 inline pipeline: decrypted credentials are streamed inline into Caddy's
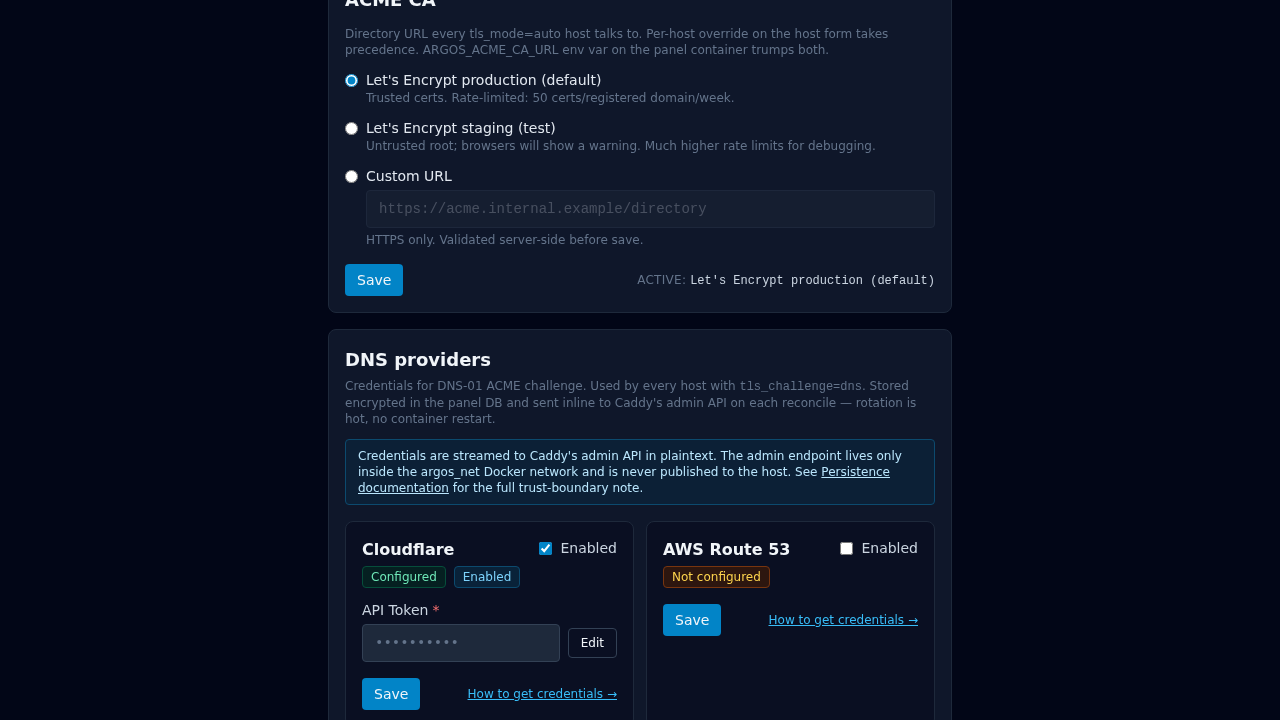
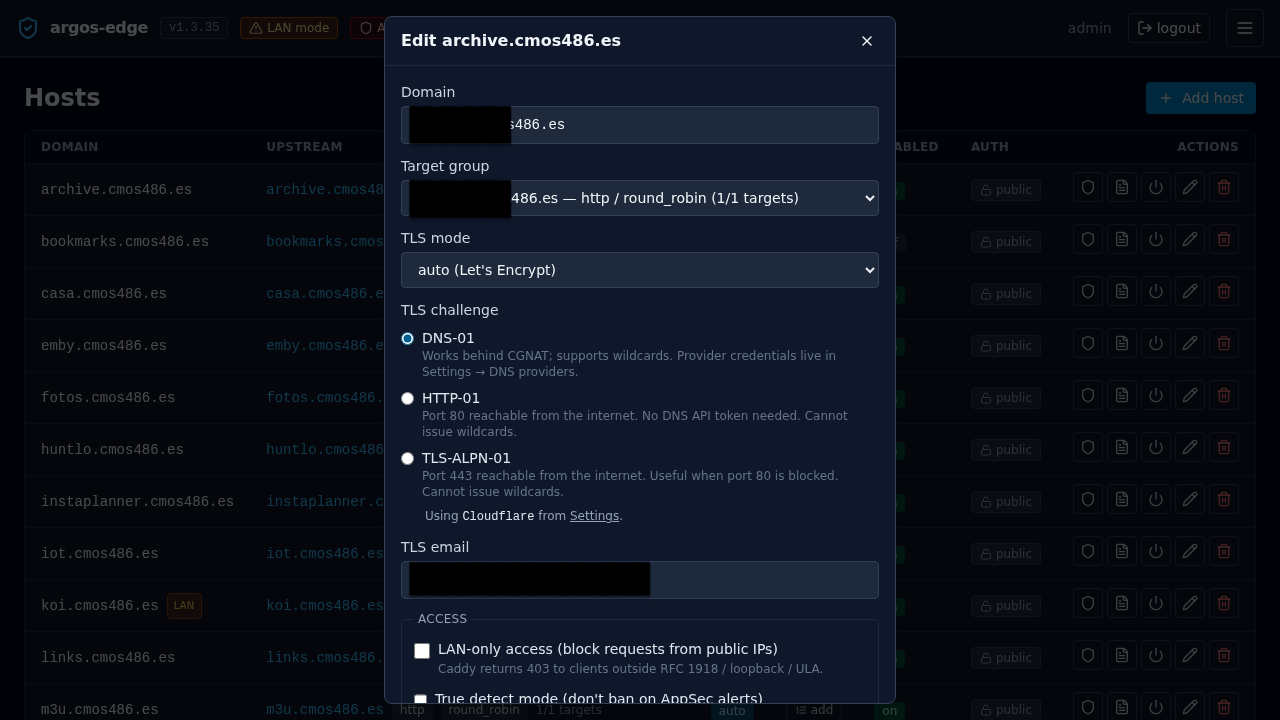
/loadJSON on every reconcile. No env-var indirection, no container restart on rotation. Save-in-UI → reconcile-automatic → new token on the next ACME order, all in the same HTTP response. - Settings → DNS providers UI for managing credentials: cards grid, enable toggles, Configured / Not-configured badges, masked secret fields with a dedicated Edit button (keeps the existing ciphertext intact when rotating siblings), inline banner surfacing Caddy's reconcile error when a saved value is rejected at
/load, "How to get credentials →" deep link per provider. - Host form DNS provider dropdown under the DNS-01 radio, with auto-selection when only one provider is enabled, a native
<select>when multiple are, and an amber warning + blocked Save when none are configured. - Drop-in migration from v1.2.x. First boot after upgrade scans for
CLOUDFLARE_API_TOKENon the panel environment and, if found AND thedns_providers.cloudflarerow has no credentials yet, encrypts the env value into the DB and flips the row to enabled. Idempotent; the env var continues to work as a fallback for one release (slated for removal in v1.4).
Breaking changes¶
None. Existing hosts keep their Cloudflare behaviour unchanged. The tls_challenge='dns' path resolves to tls_dns_provider='cloudflare' via the default backfilled by migration 025.
Migration path¶
v1.2.x → v1.3.0 is drop-in:
Migrations 024 and 025 run at startup. The cloudflare token auto-import hook runs on first boot. Subsequent reconciles switch from the {env.CLOUDFLARE_API_TOKEN} placeholder to inline DB credentials.
Operators who had a working v1.2 setup can leave .env untouched immediately; the INFO line dns_provider: imported CLOUDFLARE_API_TOKEN env var into encrypted DB shows up once during first boot post-upgrade as the signal that the env can eventually be removed.
Rollback¶
argos migrate rollback # 025: drops hosts.tls_dns_provider column
argos migrate rollback # 024: drops dns_providers table
DB-stored credentials are lost on the down migration. Operators who already removed CLOUDFLARE_API_TOKEN from .env must restore it before the rollback completes to keep Cloudflare DNS-01 working on the v1.2 code path.
Screenshots¶
Real UI captures landed in v1.3.1:
Roadmap¶
Tier 2 providers (Hetzner, DigitalOcean, Porkbun, Gandi, deSEC, OVH, DuckDNS, acme-dns) are NOT in v1.3.0. The architecture is ready for each — adding one is roughly a Dockerfile --with line + a catalogue entry + a CHECK-extension migration — and each lands on demand. See the DNS providers → Roadmap section for the tracking table and how to request a new provider.
Related¶
- DNS providers — feature reference.
- Add a host — host form walkthrough including the new provider dropdown.
- Pre-release notes (v1.3.0-alpha + v1.3.0-beta) — the incremental story, kept for history but no longer the canonical changelog for v1.3.
docs/internals/dns-providers-analysis.md— scoping analysis that justified the Tier 1 / Tier 2 split + the Option 2 inline-credentials pipeline decision.